Azure Functions networking options
1/21/202123 minutes to readThis article describes the networking features available across the hosting options for Azure Functions. All the following networking options give you some ability to access resources without using internet-routable addresses or to restrict internet access to a function app.
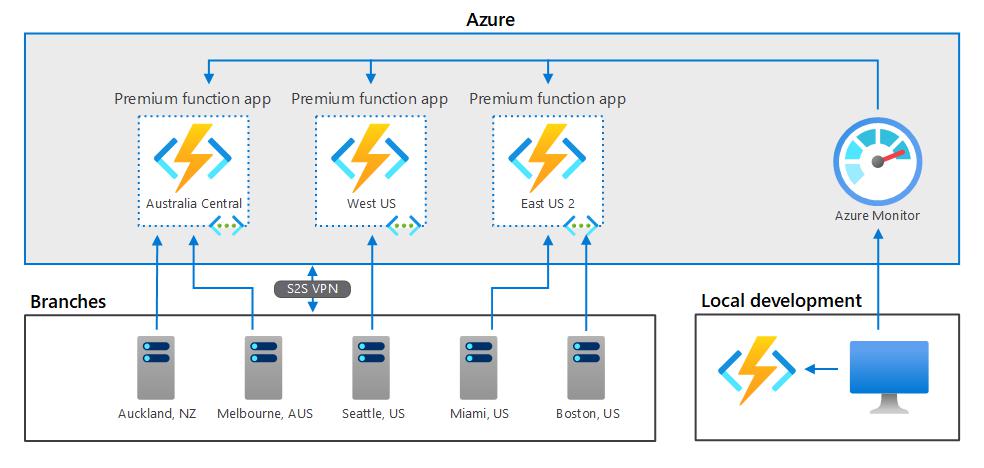
The hosting models have different levels of network isolation available. Choosing the correct one helps you meet your network isolation requirements.
You can host function apps in a couple of ways:
You can choose from plan options that run on a multitenant infrastructure, with various levels of virtual network connectivity and scaling options:The Consumption plan scales dynamically in response to load and offers minimal network isolation options.The Premium plan also scales dynamically and offers more comprehensive network isolation.The Azure App Service plan operates at a fixed scale and offersnetwork isolation similar to the Premium plan.You can run functions in an App Service Environment. This method deploys your function into your virtual network and offers full network control and isolation.You can use access restrictions to define a priority-ordered list of IP addresses that are allowed or denied access to your app. The list can include IPv4 and IPv6 addresses, or specific virtual network subnets using service endpoints. When there are one or more entries, an implicit "deny all" exists at the end of the list. IP restrictions work with all function-hosting options.
Access restrictions are available in the Premium, Consumption, and App Service.
Note
With network restrictions in place, you can deploy only from within your virtual network, or when you've put the IP address of the machine you're using to access the Azure portal on the Safe Recipients list. However, you can still manage the function using the portal.
To learn more, see Azure App Service static access restrictions.
By using service endpoints, you can restrict access to selected Azure virtual network subnets. To restrict access to a specific subnet, create a restriction rule with a Virtual Network type. You can then select the subscription, virtual network, and subnet that you want to allow or deny access to.
If service endpoints aren't already enabled with Microsoft.Web for the subnet that you selected, they'll be automatically enabled unless you select the Ignore missing Microsoft.Web service endpoints check box. The scenario where you might want to enable service endpoints on the app but not the subnet depends mainly on whether you have the permissions to enable them on the subnet.
If you need someone else to enable service endpoints on the subnet, select the Ignore missing Microsoft.Web service endpoints check box. Your app will be configured for service endpoints in anticipation of having them enabled later on the subnet.
You can't use service endpoints to restrict access to apps that run in an App Service Environment. When your app is in an App Service Environment, you can control access to it by applying IP access rules.
To learn how to set up service endpoints, see Establish Azure Functions private site access.
Azure Private Endpoint is a network interface that connects you privately and securely to a service powered by Azure Private Link.Private Endpoint uses a private IP address from your virtual network, effectively bringing the service into your virtual network.
You can use Private Endpoint for your functions hosted in the Premium and App Service plans.
When creating an inbound private endpoint connection for functions, you will also need a DNS record to resolvethe private address.By default a private DNS record will be created for you when creating a private endpoint using the Azure portal.
To learn more, see using Private Endpoints for Web Apps.
To call other services that have a private endpoint connection, such as storage or service bus, be sure to configure your app to make outbound calls to private endpoints.
Virtual network integration allows your function app to access resources inside a virtual network.Azure Functions supports two kinds of virtual network integration:
The multitenant systems that support the full range of pricing plans except Isolated.The App Service Environment, which deploys into your VNet and supports Isolated pricing plan apps.The VNet Integration feature is used in multitenant apps. If your app is in App Service Environment, then it's already in a VNet and doesn't require use of the VNet Integration feature to reach resources in the same VNet. For more information on all of the networking features, see App Service networking features.
VNet Integration gives your app access to resources in your VNet, but it doesn't grant inbound private access to your app from the VNet. Private site access refers to making an app accessible only from a private network, such as from within an Azure virtual network. VNet Integration is used only to make outbound calls from your app into your VNet. The VNet Integration feature behaves differently when it's used with VNet in the same region and with VNet in other regions. The VNet Integration feature has two variations:
Regional VNet Integration: When you connect to Azure Resource Manager virtual networks in the same region, you must have a dedicated subnet in the VNet you're integrating with.Gateway-required VNet Integration: When you connect to VNet in other regions or to a classic virtual network in the same region, you need an Azure Virtual Network gateway provisioned in the target VNet.The VNet Integration features:
Require a Standard, Premium, PremiumV2, PremiumV3, or Elastic Premium pricing plan.Support TCP and UDP.Work with Azure App Service apps and function apps.There are some things that VNet Integration doesn't support, like:
Mounting a drive.Windows Server Active Directory integration.NetBIOS.Gateway-required VNet Integration provides access to resources only in the target VNet or in networks connected to the target VNet with peering or VPNs. Gateway-required VNet Integration doesn't enable access to resources available across Azure ExpressRoute connections or work with service endpoints.
Regardless of the version used, VNet Integration gives your app access to resources in your VNet, but it doesn't grant inbound private access to your app from the VNet. Private site access refers to making your app accessible only from a private network, such as from within an Azure VNet. VNet Integration is only for making outbound calls from your app into your VNet.
Virtual network integration in Azure Functions uses shared infrastructure with App Service web apps. To learn more about the two types of virtual network integration, see:
To learn how to set up virtual network integration, see Integrate a function app with an Azure virtual network.
Using regional VNet Integration enables your app to access:
Resources in a VNet in the same region as your app.Resources in VNets peered to the VNet your app is integrated with.Service endpoint secured services.Resources across Azure ExpressRoute connections.Resources in the VNet you're integrated with.Resources across peered connections, which include Azure ExpressRoute connections.Private endpointsWhen you use VNet Integration with VNets in the same region, you can use the following Azure networking features:
Network security groups (NSGs): You can block outbound traffic with an NSG that's placed on your integration subnet. The inbound rules don't apply because you can't use VNet Integration to provide inbound access to your app.Route tables (UDRs): You can place a route table on the integration subnet to send outbound traffic where you want.By default, your app routes only RFC1918 traffic into your VNet. If you want to route all of your outbound traffic into your VNet, use the following steps to add the WEBSITE_VNET_ROUTE_ALL setting in your app:
Go to the Configuration UI in your app portal. Select New application setting.
Enter WEBSITE_VNET_ROUTE_ALL in the Name box, and enter 1 in the Value box.
Select OK.
Select Save.
Note
When you route all of your outbound traffic into your VNet, it's subject to the NSGs and UDRs that are applied to your integration subnet. When WEBSITE_VNET_ROUTE_ALL is set to 1, outbound traffic to public IP addresses is still sent from the addresses that are listed in your app properties, unless you provide routes that direct the traffic elsewhere.
Regional VNet integration isn't able to use port 25.
There are some limitations with using VNet Integration with VNets in the same region:
You can't reach resources across global peering connections.The feature is available from all App Service scale units in Premium V2 and Premium V3. It's also available in Standard but only from newer App Service scale units. If you are on an older scale unit, you can only use the feature from a Premium V2 App Service plan. If you want to make sure you can use the feature in a Standard App Service plan, create your app in a Premium V3 App Service plan. Those plans are only supported on our newest scale units. You can scale down if you desire after that.The integration subnet can be used by only one App Service plan.The feature can't be used by Isolated plan apps that are in an App Service Environment.The feature requires an unused subnet that's a /28 or larger in an Azure Resource Manager VNet.The app and the VNet must be in the same region.You can't delete a VNet with an integrated app. Remove the integration before you delete the VNet.You can have only one regional VNet Integration per App Service plan. Multiple apps in the same App Service plan can use the same VNet.You can't change the subscription of an app or a plan while there's an app that's using regional VNet Integration.Your app can't resolve addresses in Azure DNS Private Zones without configuration changes.VNet Integration depends on a dedicated subnet. When you provision a subnet, the Azure subnet loses five IPs from the start. One address is used from the integration subnet for each plan instance. When you scale your app to four instances, then four addresses are used.
When you scale up or down in size, the required address space is doubled for a short period of time. This affects the real, available supported instances for a given subnet size. The following table shows both the maximum available addresses per CIDR block and the impact this has on horizontal scale:
CIDR block sizeMax available addressesMax horizontal scale (instances)*/28115/272713/265929*Assumes that you'll need to scale up or down in either size or SKU at some point.
Since subnet size can't be changed after assignment, use a subnet that's large enough to accommodate whatever scale your app might reach. To avoid any issues with subnet capacity, you should use a /26 with 64 addresses.
When you want your apps in another plan to reach a VNet that's already connected to by apps in another plan, select a different subnet than the one being used by the pre-existing VNet Integration.
The feature is fully supported for both Windows and Linux apps, including custom containers. All of the behaviors act the same between Windows apps and Linux apps.
Regional VNet Integration enables you to reach Azure services that are secured with service endpoints. To access a service endpoint-secured service, you must do the following:
Configure regional VNet Integration with your web app to connect to a specific subnet for integration.Go to the destination service and configure service endpoints against the integration subnet.You can use network security groups to block inbound and outbound traffic to resources in a VNet. An app that uses regional VNet Integration can use a network security group to block outbound traffic to resources in your VNet or the internet. To block traffic to public addresses, you must have the application setting WEBSITE_VNET_ROUTE_ALL set to 1. The inbound rules in an NSG don't apply to your app because VNet Integration affects only outbound traffic from your app.
To control inbound traffic to your app, use the Access Restrictions feature. An NSG that's applied to your integration subnet is in effect regardless of any routes applied to your integration subnet. If WEBSITE_VNET_ROUTE_ALL is set to 1 and you don't have any routes that affect public address traffic on your integration subnet, all of your outbound traffic is still subject to NSGs assigned to your integration subnet. When WEBSITE_VNET_ROUTE_ALL isn't set, NSGs are only applied to RFC1918 traffic.
You can use route tables to route outbound traffic from your app to wherever you want. By default, route tables only affect your RFC1918 destination traffic. When you set WEBSITE_VNET_ROUTE_ALL to 1, all of your outbound calls are affected. Routes that are set on your integration subnet won't affect replies to inbound app requests. Common destinations can include firewall devices or gateways.
If you want to route all outbound traffic on-premises, you can use a route table to send all outbound traffic to your ExpressRoute gateway. If you do route traffic to a gateway, be sure to set routes in the external network to send any replies back.
Border Gateway Protocol (BGP) routes also affect your app traffic. If you have BGP routes from something like an ExpressRoute gateway, your app outbound traffic is affected. By default, BGP routes affect only your RFC1918 destination traffic. When WEBSITE_VNET_ROUTE_ALL is set to 1, all outbound traffic can be affected by your BGP routes.
After your app integrates with your VNet, it uses the same DNS server that your VNet is configured with. By default, your app won't work with Azure DNS private zones. To work with Azure DNS private zones, you need to add the following app settings:
WEBSITE_DNS_SERVER with value 168.63.129.16WEBSITE_VNET_ROUTE_ALL with value 1These settings send all of your outbound calls from your app into your VNet and enable your app to access an Azure DNS private zone. With these settings, your app can use Azure DNS by querying the DNS private zone at the worker level.
If you want to make calls to Private Endpoints, then you must make sure that your DNS lookups resolve to the private endpoint. You can enforce this behavior in one of the following ways:
Integrate with Azure DNS private zones. When your VNet doesn't have a custom DNS server, this is done automatically.Manage the private endpoint in the DNS server used by your app. To do this you must know the private endpoint address and then point the endpoint you are trying to reach to that address using an A record.Configure your own DNS server to forward to Azure DNS private zones.To provide a higher level of security, you can restrict a number of Azure services to a virtual network by using service endpoints. You must then integrate your function app with that virtual network to access the resource. This configuration is supported on all plans that support virtual network integration.
To learn more, see Virtual network service endpoints.
When you create a function app, you must create or link to a general-purpose Azure Storage account that supports Blob, Queue, and Table storage. You can replace this storage account with one that is secured with service endpoints or private endpoint.
This feature is supported for all Windows virtual network-supported SKUs in the Dedicated (App Service) plan and for the Premium plans. It is also supported with private DNS for Linux virtual network-supported SKUs. The Consumption plan and custom DNS on Linux plans aren't supported. To learn how to set up a function with a storage account restricted to a private network, see Restrict your storage account to a virtual network.
You can use Azure Key Vault references to use secrets from Azure Key Vault in your Azure Functions application without requiring any code changes. Azure Key Vault is a service that provides centralized secrets management, with full control over access policies and audit history.
If virtual network integration is configured for the app, Key Vault references may be used to retireve secrets from a network-restricted vault.
Currently, you can use non-HTTP trigger functions from within a virtual network in one of two ways:
Run your function app in a Premium plan and enable virtual network trigger support.Run your function app in an App Service plan or App Service Environment.When you run a Premium plan, you can connect non-HTTP trigger functions to services that run inside a virtual network. To do this, you must enable virtual network trigger support for your function app. The Runtime Scale Monitoring setting is found in the Azure portal under Configuration > Function runtime settings.
You can also enable virtual network triggers by using the following Azure CLI command:
az resource update -g-n /config/web --set properties.functionsRuntimeScaleMonitoringEnabled=1 --resource-type Microsoft.Web/sitesTip
Enabling virtual network triggers may have an impact on the performance of your application since your App Service plan instances will need to monitor your triggers to determine when to scale. This impact is likely to be very small.
Virtual network triggers are supported in version 2.x and above of the Functions runtime. The following non-HTTP trigger types are supported.
Important
When you enable virtual network trigger support, only the trigger types shown in the previous table scale dynamically with your application. You can still use triggers that aren't in the table, but they're not scaled beyond their pre-warmed instance count. For the complete list of triggers, see Triggers and bindings.
When your function app runs in either an App Service plan or an App Service Environment, you can use non-HTTP trigger functions. For your functions to get triggered correctly, you must be connected to a virtual network with access to the resource defined in the trigger connection.
For example, assume you want to configure Azure Cosmos DB to accept traffic only from a virtual network. In this case, you must deploy your function app in an App Service plan that provides virtual network integration with that virtual network. Integration enables a function to be triggered by that Azure Cosmos DB resource.
Hybrid Connections is a feature of Azure Relay that you can use to access application resources in other networks. It provides access from your app to an application endpoint. You can't use it to access your application. Hybrid Connections is available to functions that run on Windows in all but the Consumption plan.
As used in Azure Functions, each hybrid connection correlates to a single TCP host and port combination. This means that the hybrid connection's endpoint can be on any operating system and any application as long as you're accessing a TCP listening port. The Hybrid Connections feature doesn't know or care what the application protocol is or what you're accessing. It just provides network access.
To learn more, see the App Service documentation for Hybrid Connections. These same configuration steps support Azure Functions.
Important
Hybrid Connections is only supported on Windows plans. Linux isn't supported.
Outbound IP restrictions are available in a Premium plan, App Service plan, or App Service Environment. You can configure outbound restrictions for the virtual network where your App Service Environment is deployed.
When you integrate a function app in a Premium plan or an App Service plan with a virtual network, the app can still make outbound calls to the internet by default. By adding the application setting WEBSITE_VNET_ROUTE_ALL=1, you force all outbound traffic to be sent into your virtual network, where network security group rules can be used to restrict traffic.
To learn how to control the outbound IP using a virtual network, see Tutorial: Control Azure Functions outbound IP with an Azure virtual network NAT gateway.
The following APIs let you programmatically manage regional virtual network integrations:
The feature is easy to set up, but that doesn't mean your experience will be problem free. If you encounter problems accessing your desired endpoint, there are some utilities you can use to test connectivity from the app console. There are two consoles that you can use. One is the Kudu console, and the other is the console in the Azure portal. To reach the Kudu console from your app, go to Tools > Kudu. You can also reach the Kudo console at [sitename].scm.azurewebsites.net. After the website loads, go to the Debug console tab. To get to the Azure portal-hosted console from your app, go to Tools > Console.
In native Windows apps, the tools ping, nslookup, and tracert won't work through the console because of security constraints (they work in custom Windows containers). To fill the void, two separate tools are added. To test DNS functionality, we added a tool named nameresolver.exe. The syntax is:
nameresolver.exe hostname [optional: DNS Server]You can use nameresolver to check the hostnames that your app depends on. This way you can test if you have anything misconfigured with your DNS or perhaps don't have access to your DNS server. You can see the DNS server that your app uses in the console by looking at the environmental variables WEBSITE_DNS_SERVER and WEBSITE_DNS_ALT_SERVER.
Note
nameresolver.exe currently doesn't work in custom Windows containers.
You can use the next tool to test for TCP connectivity to a host and port combination. This tool is called tcpping and the syntax is:
tcpping.exe hostname [optional: port]The tcpping utility tells you if you can reach a specific host and port. It can show success only if there's an application listening at the host and port combination, and there's network access from your app to the specified host and port.
Debug access to virtual network-hosted resourcesA number of things can prevent your app from reaching a specific host and port. Most of the time it's one of these things:
A firewall is in the way. If you have a firewall in the way, you hit the TCP timeout. The TCP timeout is 21 seconds in this case. Use the tcpping tool to test connectivity. TCP timeouts can be caused by many things beyond firewalls, but start there.DNS isn't accessible. The DNS timeout is 3 seconds per DNS server. If you have two DNS servers, the timeout is 6 seconds. Use nameresolver to see if DNS is working. You can't use nslookup, because that doesn't use the DNS your virtual network is configured with. If inaccessible, you could have a firewall or NSG blocking access to DNS or it could be down.If those items don't answer your problems, look first for things like:
Regional VNet Integration
Is your destination a non-RFC1918 address and you don't have Route All enabled?Is there an NSG blocking egress from your integration subnet?If you're going across Azure ExpressRoute or a VPN, is your on-premises gateway configured to route traffic back up to Azure? If you can reach endpoints in your virtual network but not on-premises, check your routes.Do you have enough permissions to set delegation on the integration subnet? During regional VNet Integration configuration, your integration subnet is delegated to Microsoft.Web/serverFarms. The VNet Integration UI delegates the subnet to Microsoft.Web/serverFarms automatically. If your account doesn't have sufficient networking permissions to set delegation, you'll need someone who can set attributes on your integration subnet to delegate the subnet. To manually delegate the integration subnet, go to the Azure Virtual Network subnet UI and set the delegation for Microsoft.Web/serverFarms.Gateway-required VNet Integration
Is the point-to-site address range in the RFC 1918 ranges (10.0.0.0-10.255.255.255 / 172.16.0.0-172.31.255.255 / 192.168.0.0-192.168.255.255)?Does the gateway show as being up in the portal? If your gateway is down, then bring it back up.Do certificates show as being in sync, or do you suspect that the network configuration was changed?If your certificates are out of sync or you suspect that a change was made to your virtual network configuration that wasn't synced with your ASPs, select Sync Network.If you're going across a VPN, is the on-premises gateway configured to route traffic back up to Azure? If you can reach endpoints in your virtual network but not on-premises, check your routes.Are you trying to use a coexistence gateway that supports both point to site and ExpressRoute? Coexistence gateways aren't supported with VNet Integration.Debugging networking issues is a challenge because you can't see what's blocking access to a specific host:port combination. Some causes include:
You have a firewall up on your host that prevents access to the application port from your point-to-site IP range. Crossing subnets often requires public access.Your target host is down.Your application is down.You had the wrong IP or hostname.Your application is listening on a different port than what you expected. You can match your process ID with the listening port by using "netstat -aon" on the endpoint host.Your network security groups are configured in such a manner that they prevent access to your application host and port from your point-to-site IP range.You don't know what address your app actually uses. It could be any address in the integration subnet or point-to-site address range, so you need to allow access from the entire address range.
Additional debug steps include:
Connect to a VM in your virtual network and attempt to reach your resource host:port from there. To test for TCP access, use the PowerShell command test-netconnection. The syntax is:test-netconnection hostname [optional: -Port]Bring up an application on a VM and test access to that host and port from the console from your app by using tcpping.On-premises resourcesIf your app can't reach a resource on-premises, check if you can reach the resource from your virtual network. Use the test-netconnection PowerShell command to check for TCP access. If your VM can't reach your on-premises resource, your VPN or ExpressRoute connection might not be configured properly.
If your virtual network-hosted VM can reach your on-premises system but your app can't, the cause is likely one of the following reasons:
Your routes aren't configured with your subnet or point-to-site address ranges in your on-premises gateway.Your network security groups are blocking access for your point-to-site IP range.Your on-premises firewalls are blocking traffic from your point-to-site IP range.You're trying to reach a non-RFC 1918 address by using the regional VNet Integration feature.To learn more about networking and Azure Functions: